Résultats de recherche de titre
Articles 1 à 20 sur 3934

Mountain of Fire: Into the Heart of Volcanoes (Roberge)
Par Julie Roberge, Aless Mc, Charles Simard. 2023

Kid Olympians: True Tales of Childhood from Champions and Game Changers (Kid Legends #9)
Par Robin Stevenson. 2024
Triumphant, relatable, and totally true biographies tell the childhood stories of a diverse group of international athletes who have captured…
the world’s attention at the Summer Olympics and Paralympics, like Simone Biles, Jesse Owens, Naomi Osaka, Tatyana McFadden, and 12 other incredible olympians.Athletes throughout history have dreamed of competing in the Olympics—and some were kids themselves when those dreams and plans began! In Kid Olympians: Summer, discover the childhood stories of legends such as: Usain Bolt, who used to skip practices to go to the arcade and play video games.Serena Williams, who sometimes hit her tennis ball over the fence on purpose!Tatyana McFadden, who had to fight to be allowed on her school’s track teamFeaturing kid-friendly text and full-color illustrations, you’ll be inspired to dream bigger, faster, and higher than ever before! The diverse and inspiring group also includes Michael Phelps, Yusra Mardini, Dick Fosbury, Ibtihaj Muhammad, Gertrude Ederle, Nadia Comaneci, Ellie Simmonds, Tommie Smith, Wilma Rudolph, and Megan Rapinoe.
Pride and Persistence: Stories of Queer Activism (Do You Know My Name? #4)
Par Mary Fairhurst Breen. 2023
The activists between these pages have stood up for the queer community, whether on their own behalf or in support…
of people they love. Some made a difference by confronting injustice; others dared to be fully themselves.
See It, Dream It, Do It: How 25 people just like you found their dream jobs
Par Colleen Nelson, Kathie MacIsaac. 2023
From award-winning author Colleen Nelson, and literacy advocate Kathie MacIsaac, twenty-five profiles present a plethora of jobs, and people, making…
it easier than ever for young people to see their dreams and to live their dreams!
Beryl: The Making of a Disability Activist
Par Dustin Galer. 2023
The story of a mid-century working-class housewife whose extraordinary physical transformation empowered her to become a dynamic social activist who…
fueled a movement to create a more inclusive future for people with disabilities.
Take Control of the Mac Command Line with Terminal
Par Joe Kissell. 2022
Release your inner geek and harness the power of the Unix underpinnings to Mac OS X! This ebook from Joe…
Kissell explains everything you need to know to become comfortable working on the command line in Terminal, and provides numerous "recipes" for performing useful tasks.
Conversational Artificial Intelligence
Par Romil Rawat, Rajesh Kumar Chakrawarti, Sanjaya Kumar Sarangi, Piyush Vyas, Mary Sowjanya Alamanda, Kotagiri Srividya, Krishnan Sakthidasan Sankaran. 2024
Conversational AI combines natural language processing (NLP) with traditional software like chatbots, voice assistants, or an interactive voice recognition system…
to help customers through either a spoken or typed interface. Conversational chatbots that respond to questions promptly and accurately to help customers are a fascinating development since they make the customer service industry somewhat self-sufficient. A well-automated chatbot can decimate staffing needs, but creating one is a time-consuming process. Voice recognition technologies are becoming more critical as AI assistants like Alexa become more popular. Chatbots in the corporate world have advanced technical connections with clients thanks to improvements in artificial intelligence. However, these chatbots’ increased access to sensitive information has raised serious security concerns. Threats are one-time events such as malware and DDOS (Distributed Denial of Service) assaults. Targeted strikes on companies are familiar and frequently lock workers out. User privacy violations are becoming more common, emphasizing the dangers of employing chatbots. Vulnerabilities are systemic problems that enable thieves to break in. Vulnerabilities allow threats to enter the system, hence they are inextricably linked. Malicious chatbots are widely used to spam and advertise in chat rooms by imitating human behavior and discussions, or to trick individuals into disclosing personal information like bank account details.
Local Responses to Mine Closure in South Africa: Dependencies and Social Disruption (Routledge Studies of the Extractive Industries and Sustainable Development)
Par Sethulego Matebesi, Lochner Marais, Verna Nel. 2024
This book investigates mine closure and local responses in South Africa, linking dependencies and social disruption. Mine closure presents a…
major challenge to the mining industry and government policymakers globally, but particularly in the Global South. South Africa is experiencing notable numbers of mine closures, and this book explores the notion of social disruption, a concept often applied to describe the effects of mine growth on communities but often neglecting the impact of mine closures. The book begins with three theoretical chapters that discuss theory, closure cost frameworks and policy development in South Africa. It uses evolutionary governance theory to show how mining creates dependencies and how mining growth often blinds communities and governments to the likelihood of closure. Too easily, mining goes ahead with no concern for the possibility, or indeed inevitability, of eventual closure and how mining communities will cope. These impacts are showcased through eight place-based case studies from across South Africa, one focusing on mine workers, to demonstrate that mine closure causes significant social disruption. This book will be of interest to students and scholars researching the social impacts of mining and the extractive industries, social geography and sustainable development, as well as policymakers and practitioners working with mine closure and social impact assessments.
AI for Radiology (AI for Everything)
Par Oge Marques. 2024
Artificial intelligence (AI) has revolutionized many areas of medicine and is increasingly being embraced. This book focuses on the integral…
role of AI in radiology, shedding light on how this technology can enhance patient care and streamline professional workflows. This book reviews, explains, and contextualizes some of the most current, practical, and relevant developments in artificial intelligence and deep learning in radiology and medical image analysis. AI for Radiology presents a balanced viewpoint of the impact of AI in these fields, underscoring that AI technologies are not intended to replace radiologists but rather to augment their capabilities, freeing professionals to focus on more complex cases. This book guides readers from the basic principles of AI to their practical applications in radiology, moving from the role of data in AI to the ethical and regulatory considerations of using AI in radiology and concluding with a selection of resources for further exploration. This book has been crafted with a diverse readership in mind. It is a valuable asset for medical professionals eager to stay up to date with AI developments, computer scientists curious about AI’s clinical applications, and anyone interested in the intersection of healthcare and technology.
Computer Security – ESORICS 2023: 28th European Symposium on Research in Computer Security, The Hague, The Netherlands, September 25–29, 2023, Proceedings, Part I (Lecture Notes in Computer Science #14344)
Par Gene Tsudik, Mauro Conti, Kaitai Liang, Georgios Smaragdakis. 2024
The four-volume set LNCS 14344-14347 constitutes the refereed proceedings of the 28th European Symposium on Research in Computer Security, ESORICS…
2023, which took place in The Hague, The Netherlands, during September 25-29, 2023. The 93 full papers presented in these proceedings were carefully reviewed and selected from 478 submissions. They were organized in topical sections as follows: Part I: Crypto. Part II: Network, web and internet; privacy; and remote. Part III: Attacks; blockchain; and miscellaneous. Part IV: Machine learning; software and systems security.
This two-volume set LNCS 14465-14466 constitutes the proceedings of the 31st International Symposium on Graph Drawing and Network Visualization, GD…
2023, held in Isola delle Femmine, Palermo, Italy, in September 2023. The 31 full papers, 7 short papers, presented together with 2 invited talks, and one contest report, were thoroughly reviewed and selected from the 100 submissions. The abstracts of 11 posters presented at the conference can be found in the back matter of the volume. The contributions were organized in topical sections as follows: beyond planarity; crossing numbers; linear layouts; geometric aspects; visualization challenges; graph representations; graph decompositions; topological aspects; parameterized complexity for drawings; planar graphs; frameworks; algorithmics.
Pen Testing from Contract to Report
Par Alfred Basta, Nadine Basta, Waqar Anwar. 2024
Pen Testing from Contractto Report Protect your system or web application with this accessible guide Penetration tests, also known as…
‘pen tests’, are a means of assessing the security of a computer system by simulating a cyber-attack. These tests can be an essential tool in detecting exploitable vulnerabilities in a computer system or web application, averting potential user data breaches, privacy violations, losses of system function, and more. With system security an increasingly fundamental part of a connected world, it has never been more important that cyber professionals understand the pen test and its potential applications. Pen Testing from Contract to Report offers a step-by-step overview of the subject. Built around a new concept called the Penetration Testing Life Cycle, it breaks the process into phases, guiding the reader through each phase and its potential to expose and address system vulnerabilities. The result is an essential tool in the ongoing fight against harmful system intrusions. In Pen Testing from Contract to Report readers will also find: Content mapped to certification exams such as the CompTIA PenTest+Detailed techniques for evading intrusion detection systems, firewalls, honeypots, and moreAccompanying software designed to enable the reader to practice the concepts outlined, as well as end-of-chapter questions and case studies Pen Testing from Contract to Report is ideal for any cyber security professional or advanced student of cyber security.
Becoming SRE
Par David N. Blank-Edelman. 2024
Do you wish the existing books on site reliability engineering started at the beginning? Do you wish someone would walk…
you through how to become an SRE, how to think like an SRE, or how to build and grow a successful SRE function in your organization? Becoming SRE addresses all of these needs and more with three interconnected sections: the essential groundwork for understanding SRE and SRE culture, advice for individuals on becoming an SRE, and guidance for organizations on creating and developing a thriving SRE practice. Acting as your personal and personable guide, author David Blank-Edelman takes you through subjects like: SRE mindset, SRE culture, and SRE advocacyWhat you need to get started and hired in SRE and what the job will be like when you get thereWhat you need to bring SRE into an organization and what is required for a good organizational fit so it can thrive thereHow to work with your business folks and management around SREHow SRE can grow and mature in an organization over time Ready to become an SRE or introduce SRE into your organization? This book is here to help.
The Great Escape: A True Story of Forced Labor and Immigrant Dreams in America
Par Saket Soni. 2023
A New York Times Notable Book of 2023 Shortlisted for the 2023 Moore Prize The astonishing story of immigrants lured to the…
United States from India and trapped in forced labor—an "eye-opening" "must-read" told by the visionary labor leader who engineered their escape and set them on a path to citizenship (The New York Times Book Review). In late 2006, Saket Soni, a twenty-eight-year-old Indian-born community organizer, received an anonymous phone call from an Indian migrant worker in Mississippi. He was one of five hundred men trapped in squalid Gulf Coast &“man camps,&” surrounded by barbed wire, watched by guards, crammed into cold trailers with putrid toilets, forced to eat moldy bread and frozen rice. Recruiters had promised them good jobs and green cards. The men had scraped up $20,000 each for this &“opportunity&” to rebuild hurricane-wrecked oil rigs, leaving their families in impossible debt. During a series of clandestine meetings, Soni and the workers devised a bold plan. In The Great Escape, Soni traces the workers&’ extraordinary escape, their march on foot to Washington, DC, and their twenty-three-day hunger strike to bring attention to their cause. Along the way, ICE agents try to deport the men, company officials work to discredit them, and politicians avert their eyes. But none of this shakes the workers&’ determination to win their dignity and keep their promises to their families. Weaving a deeply personal journey with a riveting tale of twenty-first-century forced labor, Soni takes us into the lives of the immigrant workers the United States increasingly relies on to rebuild after climate disasters. The Great Escape is the gripping story of one of the largest human trafficking cases in modern American history—and the workers&’ heroic journey for justice.
The WhatsApp India Story: Inside the Digital Maya Sphere
Par Sunetra Sen Narayan, Shalini Narayanan. 2024
WhatsApp is used by over half a billion people in India today in all fields – in business, corporate and…
informal sectors, in government, for education and among friends, families and acquaintances. This book critically explores the social messaging app’s rapid expansion in India and its growing influence and looks at whether, as a form of horizontal communication, it poses a challenge to more traditional structures of communication. The book examines WhatsApp’s spread in the personal and professional lives of Indians and the myriad ways in which people in India are using the app in social and business interactions, including among people living with disabilities. Using case studies, interviews, surveys and in-depth research, it analyses key aspects of WhatsApp’s massive popularity and its impact on how people communicate. It also explores its impact on the psycho-social dynamics in India, including the dissemination of fake news and politically motivated content, and the consequent need for media regulation in the country. One of the first books to analyse the pervasiveness of WhatsApp and social media apps in different areas of Indian society, this book will be of interest to scholars and students of media studies, communication studies, digital media, cultural studies, cyberculture studies, sociology and social policy and media law.
Bitter Crop: The Heartache and Triumph of Billie Holiday's Last Year
Par Paul Alexander. 2024
A revelatory look at the tumultuous life of a jazz legend and American cultural iconIn the first biography of Billie…
Holiday in more than two decades, Paul Alexander—author of heralded lives of Sylvia Plath and J. D. Salinger—gives us an unconventional portrait of arguably America&’s most eminent jazz singer. He shrewdly focuses on the last year of her life—with relevant flashbacks to provide context—to evoke and examine the persistent magnificence of Holiday&’s artistry when it was supposed to have declined, in the wake of her drug abuse, relationships with violent men, and run-ins with the law.During her lifetime and after her death, Billie Holiday was often depicted as a down-on-her-luck junkie severely lacking in self-esteem. Relying on interviews with people who knew her, and new material unearthed in private collections and institutional archives, Bitter Crop—a reference to the last two words of Strange Fruit, her moving song about lynching—limns Holiday as a powerful, ambitious woman who overcame her flaws to triumph as a vital figure of American popular music.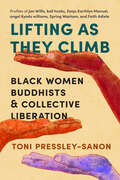
Lifting as They Climb: Black Women Buddhists and Collective Liberation
Par Toni Pressley-Sanon. 2024
The lives and writings of six leading Black Buddhist women—Jan Willis, bell hooks, Zenju Earthlyn Manuel, angel Kyodo williams, Spring…
Washam, and Faith Adiele—reveal new expressions of Buddhism rooted in ancestry, love, and collective liberation.Lifting as They Climb is a love letter of freedom and self-expression from six Black women Buddhist teachers, conveyed through the voice of author Toni Pressley-Sanon, one of the innumerable people who have benefitted from their wisdom. She explores their remarkable lives and undertakes deep readings of their work, weaving them into the broader tapestry of the African diaspora and the historical struggle for Black liberation. Black women in the U.S. have adapted Buddhist practice to meet challenges ranging from the injustices of the Jim Crow South to sexual violence, social discrimination, and bias within their Buddhist communities. Using their voices through the practice of memoir and other forms of writing, they have not only realized their own liberation but carried forward the Black tradition of leading others on the path toward collective awakening.
Las truchas están hechas de árboles
Par April Pulley Sayre. 2008
¡Las truchas realmente están hechas de árboles! Hojas y bacterias, insectos y peces, osos y personas; todos somos parte de…
un gran círculo de crecimiento, alimentación y vida –¡ahora en español!Trout are really made of trees! Leaves and bacteria, insects and fish, bears and people, too—we're all part of one big circle of growing and eating and living--now in Spanish!Un hábil matrimonio entre un texto lírico e ilustraciones de montaje energéticas, este libro explora las formas intrincadas y a menudo sorprendentes en las que las plantas y los animales están conectados en la cadena alimentaria; con texto final que describe los esfuerzos de conservación y el cuidado responsable.A deft marriage of lyrical text, and energetic collage illustrations, this book explores the intricate and often surprising ways plants and animals are connected in the food web, with back matter describing conservation efforts and responsible stewardship.
Acing the System Design Interview
Par Zhiyong Tan. 2024
The system design interview is one of the hardest challenges you&’ll face in the software engineering hiring process. This practical…
book gives you the insights, the skills, and the hands-on practice you need to ace the toughest system design interview questions and land the job and salary you want.In Acing the System Design Interview you will master a structured and organized approach to present system design ideas like: Scaling applications to support heavy traffic Distributed transactions techniques to ensure data consistency Services for functional partitioning such as API gateway and service mesh Common API paradigms including REST, RPC, and GraphQL Caching strategies, including their tradeoffs Logging, monitoring, and alerting concepts that are critical in any system design Communication skills that demonstrate your engineering maturity Don&’t be daunted by the complex, open-ended nature of system design interviews! In this in-depth guide, author Zhiyong Tan shares what he&’s learned on both sides of the interview table. You&’ll dive deep into the common technical topics that arise during interviews and learn how to apply them to mentally perfect different kinds of systems. Foreword by Anthony Asta, Michael D. Elder. About the technology The system design interview is daunting even for seasoned software engineers. Fortunately, with a little careful prep work you can turn those open-ended questions and whiteboard sessions into your competitive advantage! In this powerful book, Zhiyong Tan reveals practical interview techniques and insights about system design that have earned developers job offers from Amazon, Apple, ByteDance, PayPal, and Uber. About the book Acing the System Design Interview is a masterclass in how to confidently nail your next interview. Following these easy-to-remember techniques, you&’ll learn to quickly assess a question, identify an advantageous approach, and then communicate your ideas clearly to an interviewer. As you work through this book, you&’ll gain not only the skills to successfully interview, but also to do the actual work of great system design. What's inside Insights on scaling, transactions, logging, and more Practice questions for core system design concepts How to demonstrate your engineering maturity Great questions to ask your interviewer About the reader For software engineers, software architects, and engineering managers looking to advance their careers. About the author Zhiyong Tan is a manager at PayPal. He has worked at Uber, Teradata, and at small startups. Over the years, he has been in many system design interviews, on both sides of the table. The technical editor on this book was Mohit Kumar. Table of Contents PART 1 1 A walkthrough of system design concepts 2 A typical system design interview flow 3 Non-functional requirements 4 Scaling databases 5 Distributed transactions 6 Common services for functional partitioning PART 2 7 Design Craigslist 8 Design a rate-limiting service 9 Design a notification/alerting service 10 Design a database batch auditing service 11 Autocomplete/typeahead 12 Design Flickr 13 Design a Content Distribution Network (CDN) 14 Design a text messaging app 15 Design Airbnb 16 Design a news feed 17 Design a dashboard of top 10 products on Amazon by sales volume Appendix A Monoliths vs. microservices Appendix B OAuth 2.0 authorization and OpenID Connect authentication Appendix C C4 Model Appendix D Two-phase commit (2PC)
Blockchain Intelligent Systems: Protocols, Application and Approaches for Future Generation Computing
Par E. Golden Julie, Y. Harold Robinson, J. Jesu Vedha Nayahi, Thavavel Vaiyapuri. 2022
Blockchain provides an environment where technologies converge to provide numerous benefits. However, there are still many problems ahead, and changes…
are required at all levels - technology, algorithms, and human-computer interaction for widespread acceptance of blockchain intelligence systems. This book reviews blockchain technology and the current developments in research and business applications. It explores the real-time applications and issues that will bring the synergy needed to materialize the goal of blockchain intelligence. Researchers in various fields such as Blockchain, Data Analysis, IoT, Data Science, Crypto currencies will find this book useful. Students and professionals working on Blockchain in artificial intelligence, IoT, Healthcare, Robotics, Soft computing, and Data science will also benefit from this. It offers a realistic and thorough introduction that supports programmers, students and researchers in other disciplines. The book comprises chapters dealing with various issues, to provide readers with greater readability, versatility and adaptability.