Résultats de recherche de titre
Articles 1 à 20 sur 2924

The counterfeit countess: The jewish woman who rescued thousands of poles during the holocaust
Par Elizabeth B White. 2024
The astonishing story of Dr. Josephine Janina Mehlberg—a Jewish mathematician who saved thousands of lives in Nazi-occupied Poland by masquerading…
as a Polish aristocrat—drawing on Mehlberg's own unpublished memoir. World War II and the Holocaust have given rise to many stories of resistance and rescue, but The Counterfeit Countess is unique. It tells the remarkable, unknown story of "Countess Janina Suchodolska," a Jewish woman who rescued more than 10,000 Poles imprisoned by Poland's Nazi occupiers. Mehlberg operated in Lublin, Poland, headquarters of Aktion Reinhard, the SS operation that murdered 1.7 million Jews in occupied Poland. Using the identity papers of a Polish aristocrat, she worked as a welfare official while also serving in the Polish resistance. With guile, cajolery, and steely persistence, the "Countess" persuaded SS officials to release thousands of Poles from the Majdanek concentration camp. She won permission to deliver food and medicine—even decorated Christmas trees—for thousands more of the camp's prisoners. At the same time, she personally smuggled supplies and messages to resistance fighters imprisoned at Majdanek, where 63,000 Jews were murdered in gas chambers and shooting pits. Incredibly, she eluded detection, and ultimately survived the war and emigrated to the US. Drawing on the manuscript of Mehlberg's own unpublished memoir, supplemented with prodigious research, Elizabeth White and Joanna Sliwa, professional historians and Holocaust experts, have uncovered the full story of this remarkable woman. They interweave Mehlberg's sometimes harrowing personal testimony with broader historical narrative. Like The Light of Days , Schindler's List , and Irena's Children , The Counterfeit Countess is an unforgettable account of inspiring courage in the face of unspeakable cruelty
Lovers in auschwitz: A true story
Par Keren Blankfeld. 2024
"Mesmerizing and inspirational."—Judy Batalion, New York Times bestselling author of The Light of Days The incredible true story of two…
Holocaust survivors who fell in love in Auschwitz, only to be separated upon liberation and lead remarkable lives apart following the war—and then find each other again more than 70 years later. Zippi Spitzer and David Wisnia were captivated by each other from the moment they first exchanged glances across the work floor. It was the beginning of a love story that could have happened anywhere. Except for one difference: this romance was unfolding in history's most notorious death camp, between two young prisoners whose budding intimacy risked dooming them if they were caught. Incredibly, David and Zippi survived for years beneath the ash-choked skies of Auschwitz. Under the protection of their fellow inmates, their romance grew and deepened, even as their brushes with death mounted and David's luck in particular seemed close to running out. As the war's end finally approached and the time came for them to leave the camp, David and Zippi made plans to meet again. But neither of them could imagine how long their reunion would take or how many lives they would live in the interim. They had no inkling, either, of the betrayals that would await them along the way. But David did suspect that Zippi harbored a secret—one that could explain the mystery of his survival all those years ago. An unbelievable tale of romance, sacrifice, loss, and resilience, Lovers in Auschwitz is a saga of two young people who found themselves trapped inside a waking nightmare of the Nazis' creation, yet who nevertheless discovered a love that sustained them through history's darkest hour
Beverly hills spy: The double-agent war hero who helped japan attack pearl harbor
Par Ronald Drabkin. 2024
In the spirit of Ben Macintyre's greatest spy nonfiction, the truly unbelievable and untold story of Frederick Rutland—a debonair British…
WWI hero, flying ace, fixture of Los Angeles society, and friend of Golden Age Hollywood stars—who flipped to become a spy for Japan in the lead-up to the attack on Pearl Harbor. Frederick Rutland was an accomplished aviator, British WWI war hero, and real-life James Bond. He was the first pilot to take off and land a plane on a ship, a decorated warrior for his feats of bravery and rescue, was trusted by the admirals of the Royal Navy, had a succession of aeronautical inventions, and designed the first modern aircraft carrier. He was perhaps the most famous early twentieth-century naval aviator. Despite all of this, and due mostly to class politics, Rutland was not promoted in the new Royal Air Force in the wake of WWI. This ignominy led the disgruntled Rutland to become a spy for the Japanese navy. Plied with riches and given a salary ten times the highest-paid admiral, shuttled between Los Angeles and Tokyo where he lived in large mansions in both Beverly Hills and Yokohama, and insinuating himself into both LA high society and Japan's high command, Rutland would go on to contribute to the Japanese navy with both strategic and technical intelligence. This included scouting trips to Pearl Harbor, investigations of military preparedness, and aircraft technology. All this while living a double life, frequenting private California clubs and hosting lavish affairs for Hollywood stars and military dignitaries in his mansion on the Los Angeles Bird Streets. Supported by recently declassified FBI files and by incorporating unique and rare research through MI5 and Japanese Naval archives that few English speakers have access to, author Ronald Drabkin pieces together to completion, for the first time, this stranger-than-fiction story of one of the most fascinating and enigmatic characters of espionage history. Supplemental enhancement PDF accompanies the audiobookAims to shed new light on the past to help you make more sense of the world today. Fascinating stories…
from contributors are the leading experts in their fields, so whether they're exploring Ancient Egypt, Tudor England or the Second World War, you'll be reading the latest, most thought-provoking historical research.Aims to shed new light on the past to help you make more sense of the world today. Fascinating stories…
from contributors are the leading experts in their fields, so whether they're exploring Ancient Egypt, Tudor England or the Second World War, you'll be reading the latest, most thought-provoking historical research.Aims to shed new light on the past to help you make more sense of the world today. Fascinating stories…
from contributors are the leading experts in their fields, so whether they're exploring Ancient Egypt, Tudor England or the Second World War, you'll be reading the latest, most thought-provoking historical research.
Building a cyber risk management program: Evolving security for the digital age
Par Brian Allen. 2024
Cyber risk management is one of the most urgent issues facing enterprises today. This book presents a detailed framework for…
designing, developing, and implementing a cyber risk management program that addresses your company's specific needs. Ideal for corporate directors, senior executives, security risk practitioners, and auditors at many levels, this guide offers both the strategic insight and tactical guidance you're looking for. You'll learn how to define and establish a sustainable, defendable, cyber risk management program, and the benefits associated with proper implementation. Cyber risk management experts Brian Allen and Brandon Bapst, working with writer Terry Allan Hicks, also provide advice that goes beyond risk management. You'll discover ways to address your company's oversight obligations as defined by international standards, case law, regulation, and board-level guidance. This book helps you: understand the transformational changes digitalization is introducing, and new cyber risks that come with it; learn the key legal and regulatory drivers that make cyber risk management a mission-critical priority for enterprises; gain a complete understanding of four components that make up a formal cyber risk management program; and implement or provide guidance for a cyber risk management program within your enterprise
Grossly unsanitary living conditions, cruel and abusive treatment by camp officials, the withholding of medical treatment - these were common…
experiences for refugees imprisoned at internment camps in Britain and Canada. Walter Igersheimer's memoir exposes this bleak period in the British and Canadian war record.
The Hidden Package
Par Claire Baum. 2024
Almost forty years after the end of the war, Claire Baum opens a package from a stranger in Rotterdam, unleashing…
a flood of repressed memories from her childhood. As Claire delves into her past, she uncovers the personal sacrifice and bravery of her parents, the Dutch resistance and the families that selflessly gave shelter to her and her sister, Ollie. The Hidden Package portrays Claire’s years spent in hiding and pays tribute to all those who played a part in saving her life and ensuring a future for the next generations of her family.Introduction by Carolyne Van Der Meer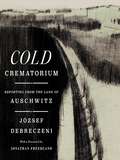
Cold crematorium: Reporting from the land of auschwitz
Par J©đzsef Debreczeni. 2024
" Cold Crematorium is an indispensable work of literature, and a historical document of unsurpassed importance. It should be required…
reading." —Jonathan Safran Foer, author of Everything Is Illuminated The first English language edition of a lost memoir by a Holocaust survivor, offering a shocking and deeply moving perspective on life within the camps—with a foreword by Jonathan Freedland. J©đzsef Debreczeni, a prolific Hungarian-language journalist and poet, arrived in Auschwitz in 1944; had he been selected to go "left," his life expectancy would have been approximately forty-five minutes. One of the "lucky" ones, he was sent to the "right," which led to twelve horrifying months of incarceration and slave labor in a series of camps, ending in the "Cold Crematorium"—the so-called hospital of the forced labor camp D©œrnhau, where prisoners too weak to work awaited execution. But as Soviet and Allied troops closed in on the camps, local Nazi commanders—anxious about the possible consequences of outright murder—decided to leave the remaining prisoners to die in droves rather than sending them directly to the gas chambers. Debreczeni recorded his experiences in Cold Crematorium , one of the harshest, most merciless indictments of Nazism ever written. This haunting memoir, rendered in the precise and unsentimental style of an accomplished journalist, is an eyewitness account of incomparable literary quality. The subject matter is intrinsically tragic, yet the author's evocative prose, sometimes using irony, sarcasm, and even acerbic humor, compels the reader to imagine human beings in circumstances impossible to comprehend intellectually. First published in Hungarian in 1950, it was never translated into a world language due to McCarthyism, Cold War hostilities and antisemitism. More than 70 years later, this masterpiece that was nearly lost to time will be available in 15 languages, finally taking its rightful place among the greatest works of Holocaust literature. A Macmillan Audio production from St. Martin's Press
Hacker culture can be esoteric, but this entertaining reference is here to help. Written by a longtime hacker, this fun…
reference introduces you to key people and companies, fundamental ideas, and milestone films, games, and magazines in the annals of hacking. From phreaking to deepfakes, and from APT (advanced package tool) to zombie malware, grasping the terminology is crucial to understanding hacker culture and history. This book from Kim Crawley (8 Steps to Better Security) is written in a conversational style and organized from A to Z. If you're just getting started on your hacker journey, you'll find plenty here to guide your learning and help you understand the references and cultural allusions you come across. More experienced hackers will find historical depth, wry humor, and some perhaps surprising facts about familiar cultural touchstones. This book will help you understand the relationship between hacker culture and cybersecurity; get to know the ideas behind the hacker ethos, like "knowledge should be free"; explore topics and publications central to hacker culture, from 2600 Magazine to Cult of the Dead Cow; appreciate the history of cybersecurity; learn about key figures in the history of hacker culture; and understand the difference between hackers and cybercriminalsAims to shed new light on the past to help you make more sense of the world today. Fascinating stories…
from contributors are the leading experts in their fields, so whether they're exploring Ancient Egypt, Tudor England or the Second World War, you'll be reading the latest, most thought-provoking historical research.
Blockchain-based Internet of Things: Opportunities, Challenges and Solutions
Par Iraq Ahmad Reshi, Sahil Sholla. 2024
This book presents an overview of the blockchain-based Internet of Things systems, along with the opportunities, challenges, and solutions in…
diverse fields such as business, education, agriculture, and healthcare. It discusses scalability, security, layers, threats, and countermeasures in blockchain-based Internet of Things network.· Elaborates on the opportunities presented by combining blockchain with artificial intelligence on the Internet of Things systems in the management of food systems, and drug supply chains.· Explains the management of computationally intensive tasks in blockchain-based Internet of Things through the development of lightweight protocols.· Presents various applications in fields including logistics and the supply chain, automobile industry, smart housing, shared economy, and agriculture.· Provides insights into blockchain-based Internet of Things systems, along with their features, vulnerabilities, and architectural flaws.· The text is primarily written for graduate students, and academic researchers working in the fields of computer science and engineering, electrical engineering, and information technology.
This book unveils the most advanced techniques and innovative applications in the natural language processing (NLP) field. It uncovers the…
secrets to enhancing language understanding, and presents practical solutions to different NLP tasks, as text augmentation, paraphrase generation, and restoring spaces and punctuation in multiple languages. It unlocks the potential of hierarchical multi-task learning for cross-lingual phoneme recognition, and allows readers to explore more real-world applications such as error correction, aggregating industrial security findings as well as predicting music emotion values from social media conversations. "Practical Solutions for Diverse Real-World NLP Applications" is the suitable guidebook for researchers, students, and practitioners as it paves the way for them by delivering invaluable insights and knowledge.
Computer Science and Educational Informatization: 5th International Conference, CSEI 2023, Kunming, China, August 11–13, 2023, Revised Selected Papers, Part II (Communications in Computer and Information Science #1900)
Par Jianhou Gan, Yi Pan, Juxiang Zhou, Dong Liu, Xianhua Song, Zeguang Lu. 2024
These two volumes constitute the revised selected papers of the 5th International Conference, CSEI 2023, held in Kunming, China, during…
August 11–13, 2023.The 76 full papers and the 21 short papers included in this volume were carefully reviewed and selected from 297 submissions. They focus on computer science, education informatization and engineering education, innovative application for the deeper integration of education practice and information technology, educational informatization and big data for education.
Optimising NMR Spectroscopy Through Method and Software Development (Springer Theses)
Par Jonathan Yong. 2024
This book provides a comprehensive overview of Nuclear Magnetic Resonance (NMR) theory, its applications, and advanced techniques to improve the…
quality and speed of NMR data acquisition. In this book, the author expands his outstanding Ph.D. thesis and provides a valuable resource for researchers, professionals, and students in the field of NMR spectroscopy. The book covers quantum mechanics basics, and topics like density operators, pulse sequences, 1D pulse acquisition, INEPT (Insensitive nuclei enhancement by polarization transfer), product operators, and 2D NMR principles. It also explores innovative experiments like States HSQC (Heteronuclear Single Quantum Coherence) and echo-antiecho HSQC with gradients. In the subsequent chapters, the author discusses Pure Shift NMR, including PSYCHE (Pure Shift Yielded by Chirp Excitation) and its optimizations, such as waveform parameterization and time-reversal methods. The 'Discrete PSYCHE' approach and Ultrafast PSYCHE-iDOSY (Diffusion-ordered spectroscopy) are also highlighted. This book presents the POISE (Parameter Optimisation by Iterative Spectral Evaluation) software for real-time NMR experiment optimization, including pulse width calibration and Ernst angle optimization, and demonstrates applications across various NMR experiments. Lastly, the book examines accelerated 2D NMR data collection and the NOAH (NMR by Ordered Acquisition using 1H detection) supersequences, emphasizing automated pulse program creation using GENESIS (GENEration of Supersequences In Silico). Covered NMR experiments include 13C sensitivity-enhanced HSQC, 15N HMQC (Heteronuclear Multiple Quantum Coherence), dual HSQC, HSQC-TOCSY (Total Correlation Spectroscopy), HMBC (Heteronuclear Multiple Bond Correlation), and ADEQUATE (Adequate Sensitivity Double-Quantum Spectroscopy).
Information and Software Technologies: 29th International Conference, ICIST 2023, Kaunas, Lithuania, October 12–14, 2023, Proceedings (Communications in Computer and Information Science #1979)
Par Audrius Lopata, Daina Gudonienė, Rita Butkienė. 2024
This book constitutes the refereed proceedings of the 29th International Conference on Information and Software Technologies, ICIST 2023, held in…
Kaunas, Lithuania, in October 2023.The 27 full papers included in this volume were carefully reviewed and selected from 75 submissions. These proceedings contain a diverse array of research and insights in the field of Information Technology and related areas, such as: intelligent systems and software engineering advances, intelligent methods for data analysis and computer aided software engineering, language technologies and smart e-learning applications, AI-based it solutions.
Continuous Biometric Authentication Systems: An Overview (SpringerBriefs in Computer Science)
Par Max Smith-Creasey. 2024
This book offers an overview of the field of continuous biometric authentication systems, which capture and continuously authenticate biometrics from…
user devices. This book first covers the traditional methods of user authentication and discusses how such techniques have become cumbersome in the world of mobile devices and short usage sessions. The concept of continuous biometric authentication systems is introduced and their construction is discussed. The different biometrics that these systems may utilise (e.g.: touchscreen-gesture interactions) are described and relevant studies surveyed. It also surveys important considerations and challenges.This book brings together a wide variety of key motivations, components and advantages of continuous biometric authentication systems. The overview is kept high level, so as not to limit the scope to any single device, biometric trait, use-case, or scenario. Therefore, the contents of this book are applicable to devices ranging from smartphones to desktop computers, utilising biometrics ranging from face recognition to keystroke dynamics. It also provides metrics from a variety of existing systems such that users can identify the advantages and disadvantages of different approaches.This book targets researchers and lecturers working in authentication, as well as advanced-level students in computer science interested in this field. The book will also be of interest to technical professionals working in cyber security.
This book constitutes revised papers from the International Workshops held at the 21st International Conference on Business Process Management, BPM…
2023, in Utrecht, The Netherlands, during September 2023.Papers from the following workshops are included:• 7th International Workshop on Artificial Intelligence for Business Process Management (AI4BPM 2023)• 7th International Workshop on Business Processes Meet Internet-of-Things (BP-Meet-IoT 2023)• 19th International Workshop on Business Process Intelligence (BPI 2023)• 16th International Workshop on Social and Human Aspects of Business Process Management (BPMS2 2023)• 2nd International Workshop on Data-Driven Business Process Optimization (BPO 2023)• 11th International Workshop on Declarative, Decision and Hybrid Approaches to Processes (DEC2H 2023)• 1st International Workshop on Digital Twins for Business Processes (DT4BP 2023)• 1st International Workshop on Formal Methods for Business Process Management (FM-BPM 2023) • 2nd International Workshop on Natural Language Processing for Business Process Management (NLP4BPM 2023)• 1st International Workshop on Object-Centric Processes from A to Z (OBJECTS 2023)• 3rd International Workshop on Change, Drift, and Dynamics of Organizational Processes (ProDy 2023) Each of the workshops focused on particular aspects of business process management. Overall, after a thorough review process, 42 full papers were selected from a total of 86 submissions.